I am an indirect reseller (Tier 2) and I recently ordered an Azure subscription from our Indirect provider for our existing customer's tenant with approved GDAP roles but when I entered service management via Partner Center and open Azure Portal I didn't see any subscription available.
The subscription was deployed and I saw it when I was using the Global Admin account in the customer's tenant (domain .onmicrosoft.com). At the same time, I was unable to see the same subscription with the GDAP technician account. This was a decent blocker.
I was expecting I could solve it myself because what else than double Global admin would be needed? It ended up with the indirect provider being the side to fix it by making the subscription accessible. The keyword for the whole operation is "include the indirect reseller".
Partner with indirect resellers in the Cloud Solution Provider program - Partner Center | Microsoft Learn
Well, I thought at first it would be enough. But no, still no change. The next keyword to follow is "AOBO" which stands for 'Admin on Behalf of' and it is briefly explained in the article:
Workloads supported by granular delegated admin privileges (GDAP) - Partner Center | Microsoft Learn
But what I found explaining even better was this CSP dev video (from 17:45 onwards).
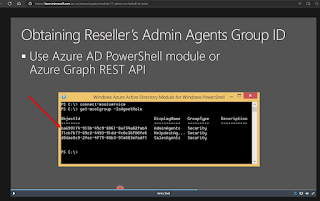
Subscription owner role needs to be set via Powershell (only) for a groupID that exists with AdminAgents GDAP role in Tier2's PartnerCenter by a user with global admin or similar elevated permissions based on the customer's tenant.
The commands are following
- Install-Module -Name AzureAD
- Connect-AzureRmAccount
- Get-AzureRmSubscription
- New-AzureRmRoleAssignment
So good old Powershell only magic in Azure. After configuring that the subscription is normally visible to all Partner tenant users so I could get back to the actual assignment.
Note: if you don't see subscription even with the customer tenant account then you might want to use this elevation trick in Entra: